How Enterprise .NET Applications Manage Secrets with Azure Key Vault
Introduction
Most applications rely on sensitive configuration values such as database credentials, API tokens, or service authentication keys.
In many projects these values are stored in:
-
appsettings.json -
web.config -
environment variables
While this works during development, it creates risks in real-world environments. Secrets can accidentally be committed to source control, duplicated across environments, or exposed in shared hosting environments.
A better approach is to separate secret storage from application configuration. Azure Key Vault provides this capability.
What is Azure Key Vault
Azure Key Vault is a cloud service designed to securely store and control access to sensitive application data.
Instead of embedding secrets in application files, applications retrieve them securely from the vault when needed.
Key Vault supports three primary types of data.
Secrets
Secrets are commonly used application values such as:
-
connection strings
-
API tokens
-
storage account keys
Keys
Cryptographic keys used for encryption and signing operations.
Certificates
TLS/SSL certificates that applications use for secure communication.
Why Applications Use Key Vault
Large applications use Key Vault for several reasons.
Centralized management
Secrets are stored in a single secure location.
Access control
Applications and services access secrets through Azure identity.
Secret rotation
Credentials can be updated without modifying application code.
Security isolation
Secrets are removed from application configuration files.
Authentication Options
Applications must authenticate with Azure before accessing the vault.
Common authentication approaches include the following.
Azure CLI Authentication
Used mostly during development.
az loginThe application uses the logged-in developer identity to access Azure resources.
ClientId / ClientSecret / TenantId
This method uses an Azure App Registration (Service Principal).
Typical configuration values include:
KeyVault__ClientId
KeyVault__ClientSecret
This approach works across many environments but requires protecting the client secret.
Managed Identity
Managed Identity is the preferred option for applications running in Azure.
The Azure platform automatically provides the identity used to access the vault, eliminating the need to store credentials.
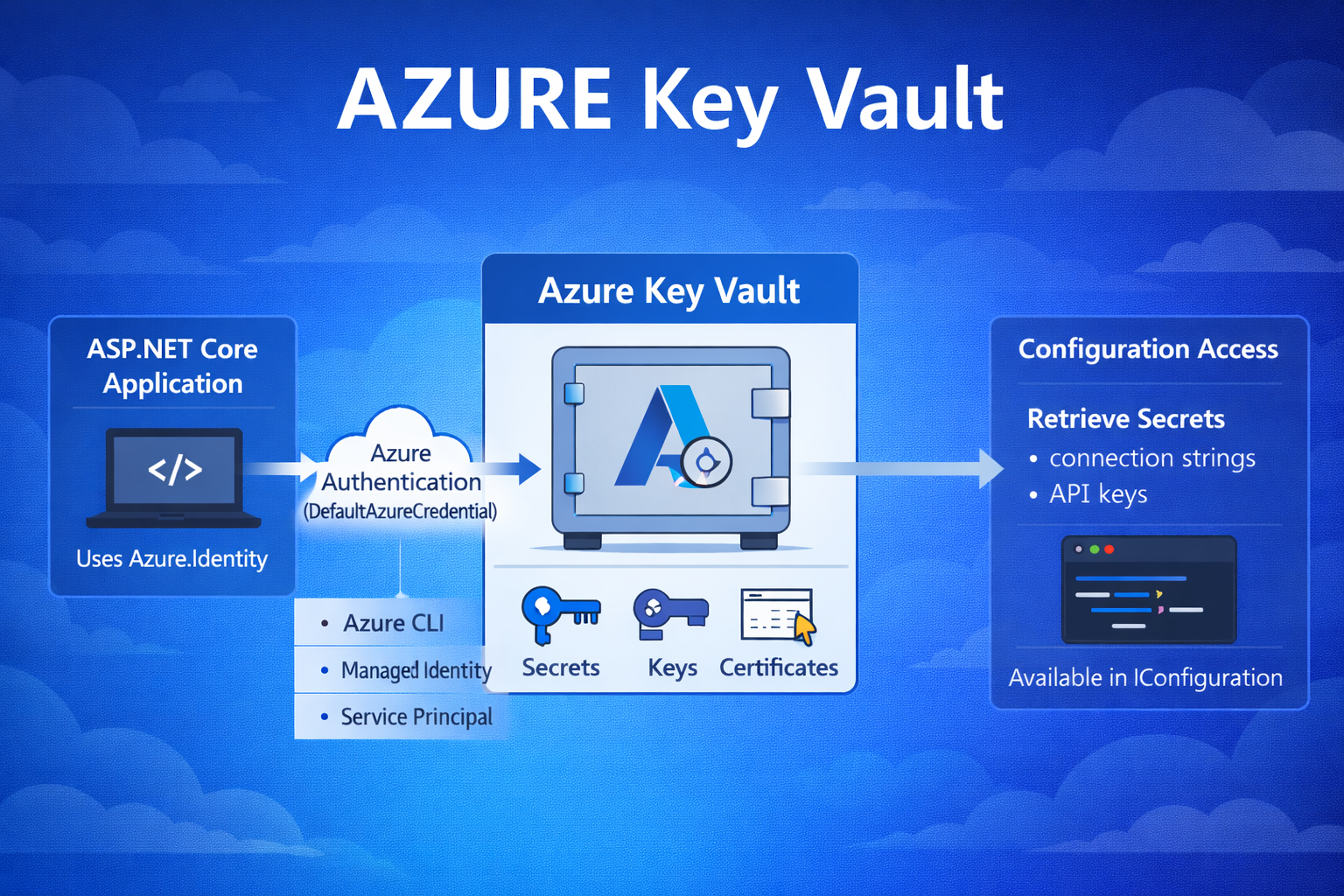
Architecture Flow
A typical flow for retrieving secrets looks like this:
Application start → Authentication → Key Vault → Secret retrieval → Configuration system
Architecture Diagram Description
│
│ Azure.Identity
▼
Authentication (DefaultAzureCredential)
│
▼
Azure Key Vault
│
▼
Secrets injected into IConfiguration
Implementation in ASP.NET Core
Install Required NuGet Packages
Azure.Security.KeyVault.Secrets
Azure.Extensions.AspNetCore.Configuration.Secrets
These libraries enable authentication and integration with the ASP.NET Core configuration system.
Configure Key Vault in Program.cs
Key Vault can be added as a configuration provider.
Once registered, secrets stored in the vault become available through IConfiguration.
How DefaultAzureCredential Works
DefaultAzureCredential automatically attempts multiple authentication methods.
Typical order includes:
-
Environment credentials
-
Managed Identity
-
Azure CLI login
This allows the same application code to work both locally and in Azure environments.
Reading Secrets from Key Vault
Secrets stored in Key Vault can be accessed directly from configuration.
var connectionString = configuration["DbConnection"];If a secret with the same name exists in the vault, the configuration provider retrieves it automatically.
Verifying Secrets
Developers can confirm secret values using the Azure CLI.
az keyvault secret show --name DbConnection --vault-name your-vault-name
Secrets can also be viewed directly in the Azure Portal → Key Vault → Secrets section.
Security Best Practices
When using Azure Key Vault:
-
Never store secrets in Git repositories
-
Prefer Managed Identity in production environments
-
Rotate credentials periodically
-
Restrict vault access using RBAC permissions
Developer Workflow Diagram
│
│ az login
▼
Run ASP.NET Core Application
│
▼
DefaultAzureCredential
│
▼
Azure Key Vault
│
▼
Secret returned to application
Azure Key Vault is an important part of building secure cloud applications. By removing secrets from configuration files and storing them in a centralized vault, applications gain better security, easier credential management, and improved operational control.
When combined with Azure Identity and Managed Identity, Key Vault provides a clean and secure approach for managing secrets in ASP.NET Core applications.

